In this tutorial we will be covering dynamic malware analysis tools which are being used to determine the behaviour of malware after it has been executed. This tutorial is part 2 of 6 in our Malware Analysis tutorials on www.hackingtutorials.org. If you haven’t read part 1 of this series please read it first before continuing on this malware analysis tutorial.
In this tutorial we will be covering Dynamic Malware Analysis Tools which are used to analyse activity after the execution of malware in virtual machines. We will be looking at tools like Procmon, Process Explorer, Regshot, ApateDNS, Netcat, Wireshark and INetSim to analyse the malware. Dynamic Malware Analysis is typically performed after static malware analysis has reached a dead end. You will reach a dead end quickly when malware is packed or obfuscated for example. Dynamic Malware Analysis is also a great way to identify the type of malware quickly, if you are facing Ransomware you will notice the encrypted files and forced payment methods quickly after executing the malware.
Dynamics Malware Analysis Risks
Please be aware of the fact that Dynamic Malware Analysis can put your system and network at risk, you will be executing real malware to analyse it’s behaviour. We advise you to only execute malware on virtual machines or dedicated systems in isolated networks which are not connected to the internet. We do not need an internet connection on our malware analysis machine since there are serveral tools available for simulating an internet connection. We will be covering a few of these tools in this article. Even though we’re executing the malware in virtual machines, it is not guaranteed that the host or your network is perfectly safe because malware developers always find surprising new ways for infection and make malware analysis harder to perfom.
Dynamic Malware Analysis Tools
As already mentioned we’ll be looking at the following tools for dynamic malware analysis: Procmon, Process Explorer, Regshot, ApateDNS, Netcat, Wireshark and INetSim. For your convenience we will supply a download link for the tools. We will be updating this list along the way so be sure to subscribe to our newsletter.
Procmon
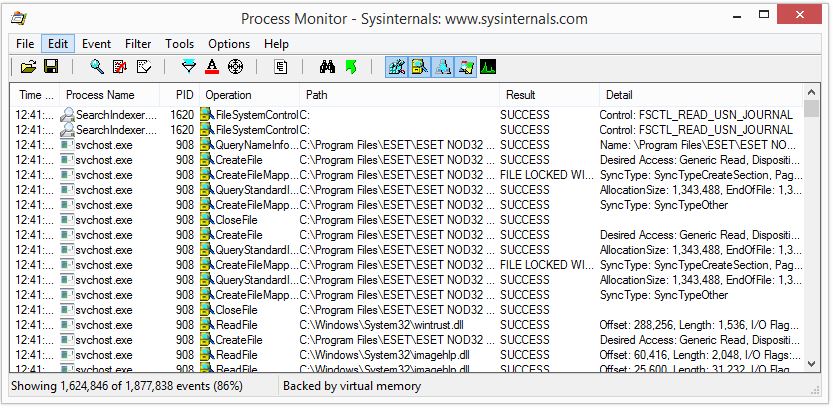
Procmon, or Process Monitor, is a free tool developed by Windows SysInternals and is used to monitor the Windows filesystem, registry and process activity real-time. The tool is a combination of 2 legacy tools; FileMon and RegMon. Procmon has some great features added on top of FileMon and Procmon like non-destructive filtering of data and boottime logging. Non-destructive filtering means that all data is captured but only filtered data is displayed to the user.
The latest version of Process Monitor is version 3.2 which can be downloaded here.
Process Explorer
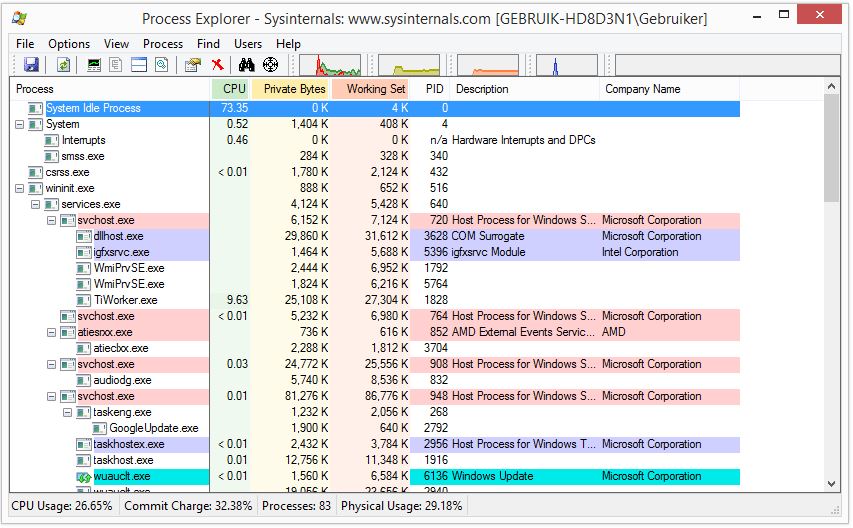
Process Explorer is also a free tool available from Microsoft which should be running when performing Dynamic Malware Analysis. Process Explorer is used to monitor the running processes and shows you which handles and DLL’s are running and loaded for each process.
The latest version of Process Explorer can be downloaded here.
Regshot

Regshot is a great open source utility to monitor your registry for changes by taking a snapshot which can be compared to the current state of your registry. This allows you to see the changes made to your registry after the malware has been executed on your system.
The latest version of Regshot is available for download here.
ApateDNS
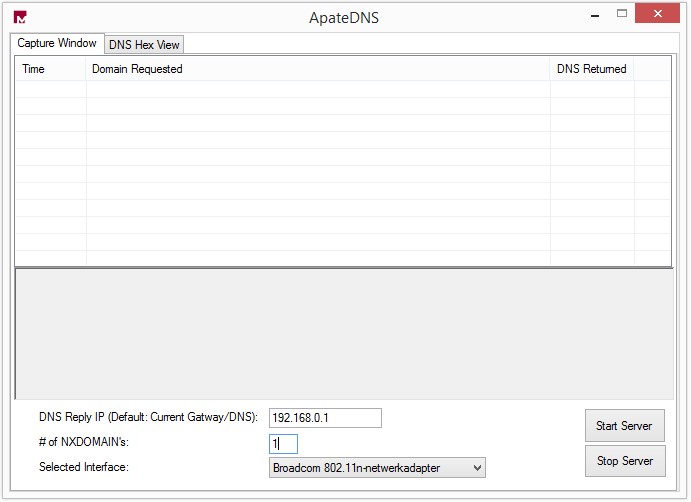
Another great tool for performing Dynamic Malware Analysis is ApateDNS. ApateDNS is a tool for controlling DNS responses and acts as a DNS server on your local system. ApateDNS will spoof DNS responses to DNS requests generated by the malware to a specified IP address on UDP port 53. The IP address or hostname is often retrieved from the malware by performing static malware analysis, for example by examining the resources sections, or by using sandboxes. ApateDNS is also capable of recovering multiple domains using the NXDOMAIN parameter since malware often tries multiple hosts to connect to.
ApateDNS is available from FireEye and can be downloaded using the following link: ApateDNS.
Netcat
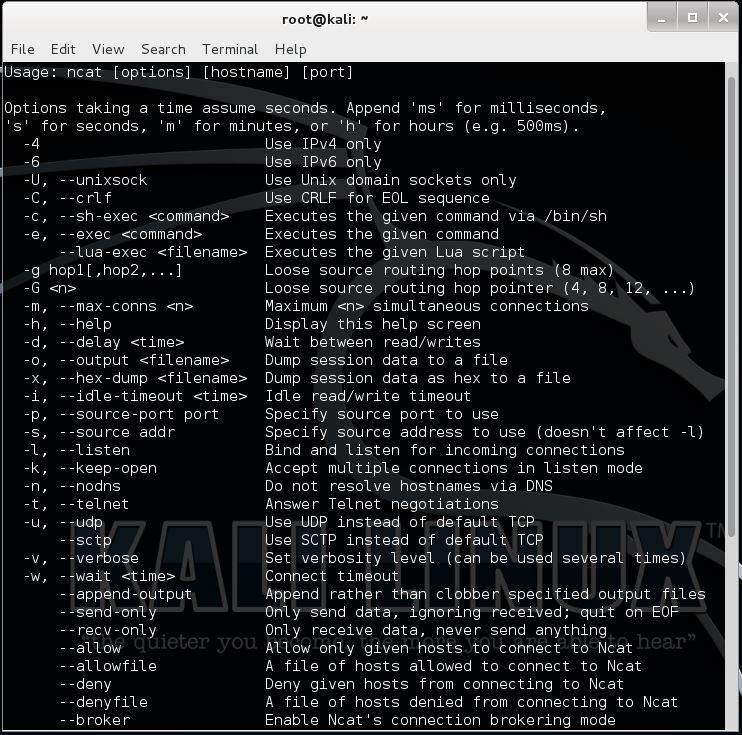
Netcat, ncat or just simply nc is a tool used to read and write to network connections using TCP and UDP. Netcat is also called the Swiss Army Knife because of the many features it offers like: port scanning, port forwarding, tunneling, proxying and a lot more. Netcat is a great tool to perform Dynamic Malware Analysis because it can make almost any network connection a malware analyst might ever need. Netcat can be used to make inbound and outbound connections on any port and can be used in client mode for connecting and in server mode for listening.
A lot of malware communicates over port 80 (HTTP) and 443 (HTTPS) because on most systems these ports are not blocked by a firewall. When performing Dynamic Malware Analysis we could use ApateDNS to redirect a DNS request made by the malware to a host which is running Netcat in servermode listening to the specified IP address on the specified port. This way we can monitor the requests made by malware using ApateDNS for redirecting requests and Netcat for monitoring the requests. In the Dynamic Malware Analysis tutorials we will be covering the use of ApateDNS and Netcat in more detail.
Netcat can be downloaded from the Nmap website here and is also included in Kali Linux.
Wireshark
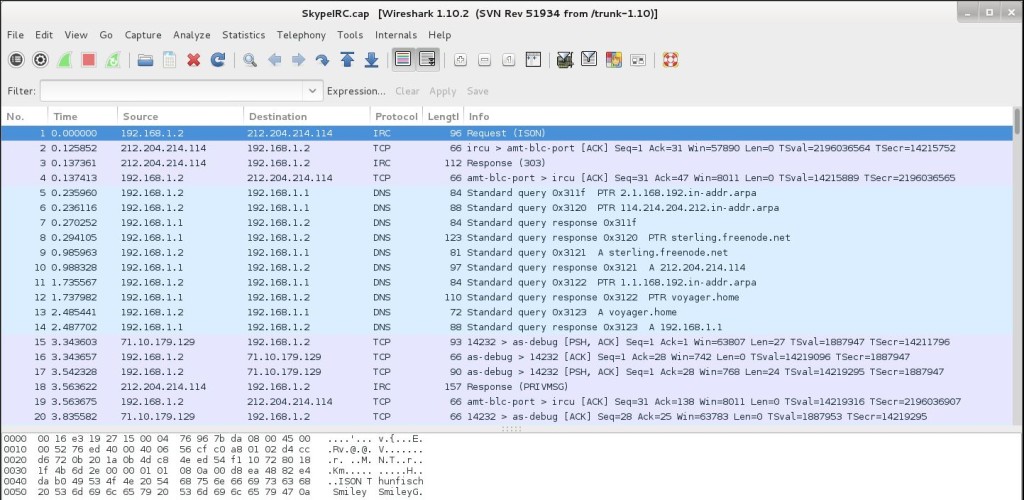
Wireshark is one of the best network protocol analyser tools available, if not the best. If you didn’t know Wireshark you probably wouldn’t be reading this article about Dynamic Malware Analysis. Wireshark is used to analyse a network to the greatest detail to see what is currently happening and capture packets to files. Wireshark can be used for live packet capturing, deep inspection of hundreds of protocols, browse and filter packets and is multiplatform. When performing Dynamic Malware Analysis Wireshark can be used to inspects packets and log network traffic to files.
Wireshark is included with Kali Linux but also available for Windows and Mac. Wireshark can be downloaded here.
INetSim
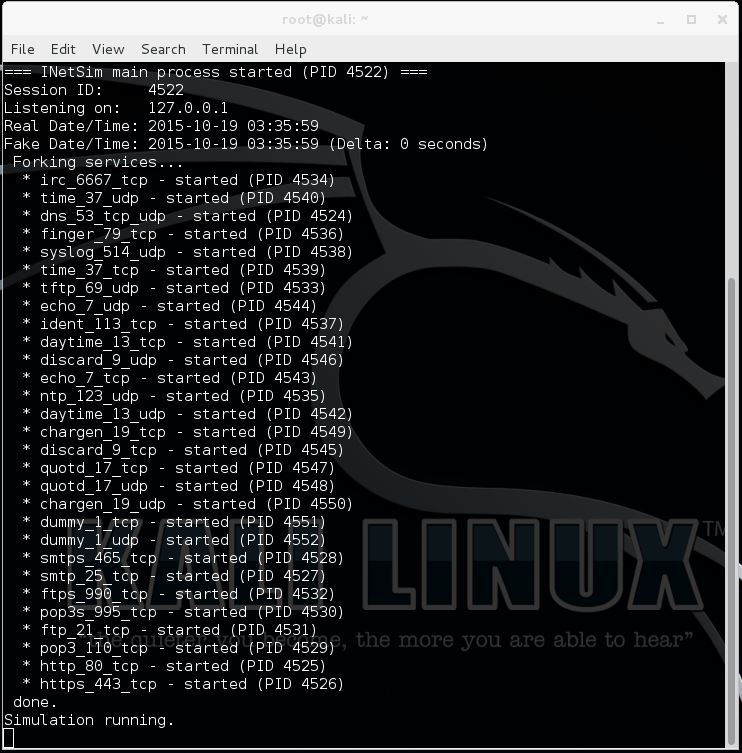
INetSim is a Linux based tool build for Malware Analysis to simulate the most common internet services like http, https, DNS, FTP and many more. When performing Dynamic Malware Analysis on a windows machine you can use a virtual machine in the same network as you malware analysis machine to run INetSim. INetSim fakes the common internet services which malware might use and answers the requests made accordingly. For example when malware requests a file, INetSim will return the file. When malware scans a webserver, INetSim will return a Microsoft IIS webserver banner in order to keep the malware running. INetSim will also log all incoming connections so you can analyse which services the malware is using and what requests it makes. INetSim is also highly configurable, when a malware uses a non-standard port for a service, you can change the listener port on a specific service in INetSim. We will be covering INetSim in more detail in the Malware Analysis Tutorials on www.hackingtutorials.org in a little while.
INetSim 1.2.5 is the current version which is included with Kali Linux 2.0 and can be downloaded here.
More Dynamic Malware Analysis Tools
Needless to say is that we covered just a few of the Dynamic Malware Analysis Tools available. In the upcoming few days we will be adding more tools for you to download and explore so be sure to subscribe to Hacking Tutorials to stay informed about updates. If you have any questions regarding the tools we encourage you to ask them here. Also let us know when you have suggestions for other tools. You can do so by replying to this post.
- Basic Malware Analysis Tools
- Dynamic Malware Analysis Tools
- Malware Types Explained
- Basic Malware Analysis
- Advanced Static Malware Analysis
- Advanced Dynamic Malware Analysis
Thanks for reading and see you in the next chapter: Different kinds of Malware.
If you’re interested in learning more about reverse engineering, malware analysis and exploits, you can follow any of these online courses:
Online Hacking Courses
Penetration Testing Course + Labs

Reverse Engineering and Exploit Development
Application Penetration Testing for Security Professionals. Read more…

Windows Exploit Development Megaprimer
Learn how to write reliable exploits.
Read more…

3 Comments
Can you send me a link to clean malware on an android Huawei smart phone please I am desperate and its urgent pm me please and thank you in advance
I’m sorry but I can’t help you with that.
Where are the debuggers? I’m interested in the rest of this article series very nice work!