In this article we will be talking about the very basics of Metasploit and the Metasploit commands used in the command line interface. At first the MSF console command line and the number of available commands might seem a lot and hard to understand and use, but don’t be intimidated by them. Once you get to understand the concept and the clear structure it will be very easy. If we put it all together the Metasploit framework consists of the core and base, a lot of exploits, payloads, modules (Ruby classes), plugin’s, scripts and multiple user interfaces. Metasploit framework also contains some great information gathering tools called auxiliary modules. Auxiliary modules can be used for port scanning, service identification, password sniffing and Windows patch enumeration. Metasploit is highly customizable for advanced users and can be customized the meet your custom needs by writing your own exploits, modules, plugin’s and scripts. If Metasploit doesn’t provide the information gathering module you need by default, than you can simply write it yourself.
The msfconsole is the user interface known to be the most stable interface and the one we will be working with throughout the Metasploit tutorials on Hacking Tutorials. Apart from the stability, another benefit of the msfconsole is the option to execute external commands like the ping command and the tab auto completion. There is also a graphical user interface available for Metasploit called Armitage. We will be looking at Armitage and how to use it instead of msfconsole in a later tutorial. Let’s continue this Metasploit commands tutorial with updating the Metasploit Framework if necessary and then switch to the msfconsole to see what commands are available to us.
Basic Msfconsole commands
Assuming you are on Kali Linux 2016 rolling edition we can start the Metasploit framework and msfconsole by clicking the Metasploit icon in the dock. This will start the PostgreSQL service and Metasploit service automatically.
Updating Metasploit with msfupdate
Let’s start with updating Metasploit by using the following command in a terminal session (not in msfconsole):
msfupdate
This command should update the Metasploit framework to the latest version. The updates says that we should be expecting updates weekly(ish). Beware: Running msfupdate might break your Metasploit installation. After running this command for this tutorial we ran into errors like:
An error occurred while installing pg (0.18.3), and Bundler cannot continue.
Make sure that gem install pg -v '0.18.3' succeeds before bundling.
This error had something to do with PostgreSQL and to fix this problem first try to run the following commands:
apt-get update
apt-get upgrade
apt-get dist-upgrade
This solved to problem on our side, it probably had something to do with an outdated version of a package. Is your Metasploit installation broken after running an update and you need some help to fix it? Use the comment function below and we’ll try to help you as best as we can. Let’s continue with the msfconsole.
Metasploit msfconsole
When Metasploit has booted and the msfconsole is available we can type ‘help’ to get an overview of the Metasploit core and backend commands with a description:
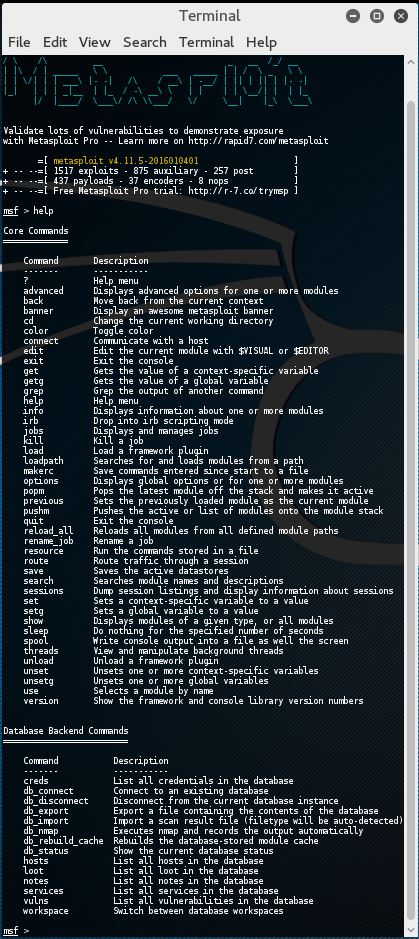
It would be a waste of time and outside the scope of this tutorial to explain every single Metasploit command in this tutorial. We just want you to be up and running as soon as possible in Metasploit and therefore a basic knowledge of basics commands should be sufficient for the moment. You will learn a lot more about the advanced options along the way. Also, most command descriptions should be very clear about what the command exactly does and how to use it. For now we will be looking at the most used basic Metasploit commands in this tutorial like:
- Basic commands: search, use, back, help, info and exit.
- Exploit commands: set to set variables and show to show the exploit options, targets, payloads, encoders, nops and the advanced and evasion options.
- Exploit execution commands: run and exploit to run exploits against a target.
There is also a comprehensive Metasploit documentation included with Metasploit which can be used to clarify anything. Let’s have a look at the Metasploit commands.
Metasploit commands
We will go through the Metasploit basic commands quickly so we can get started with the fun part and learn how to use the exploits on a vulnerable machine like Metasploitable 2. The basics command consist of help, back, exit and info.
Use, back and exit commands
The use command in Metasploit is used to activate a particular module and changes the context of the msfconsole to that particular module. The exploit name will be mentioned in red on the command line as following:
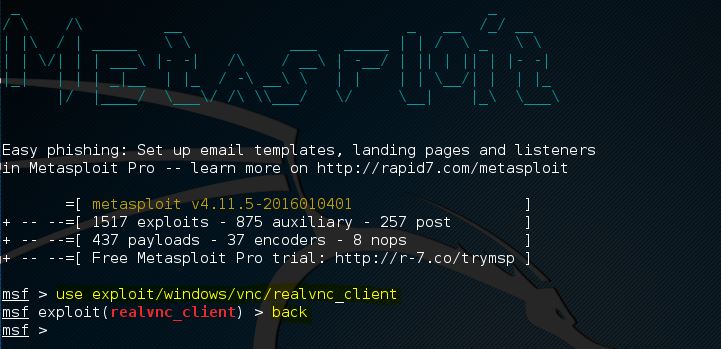
In this example we have changed the context of the command line to the exploit called realvnc_client. From here on we can retrieve information about this exploit, set the required exploit parameters and run it against a target.
If we want to leave the exploit context and switch back to the msfconsole we need to use the back command. The back command will take us back to the msfconsole in the general context. From here on we can issue the use command again to switch to another Metasploit module.
The exit command will close the msfconsole and will take you back to the Kali Linux terminal.
Help command
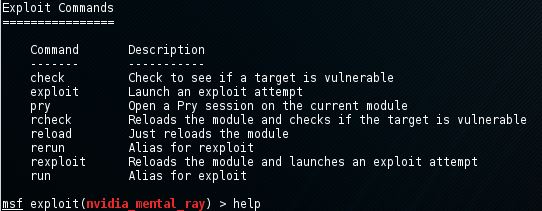
As we’ve seen earlier in this tutorial the help command will return a list of possible commands together with a description when typed at the msfconsole. When there is an active exploit selected we can use the help command to get a list of exploit commands:
Info command
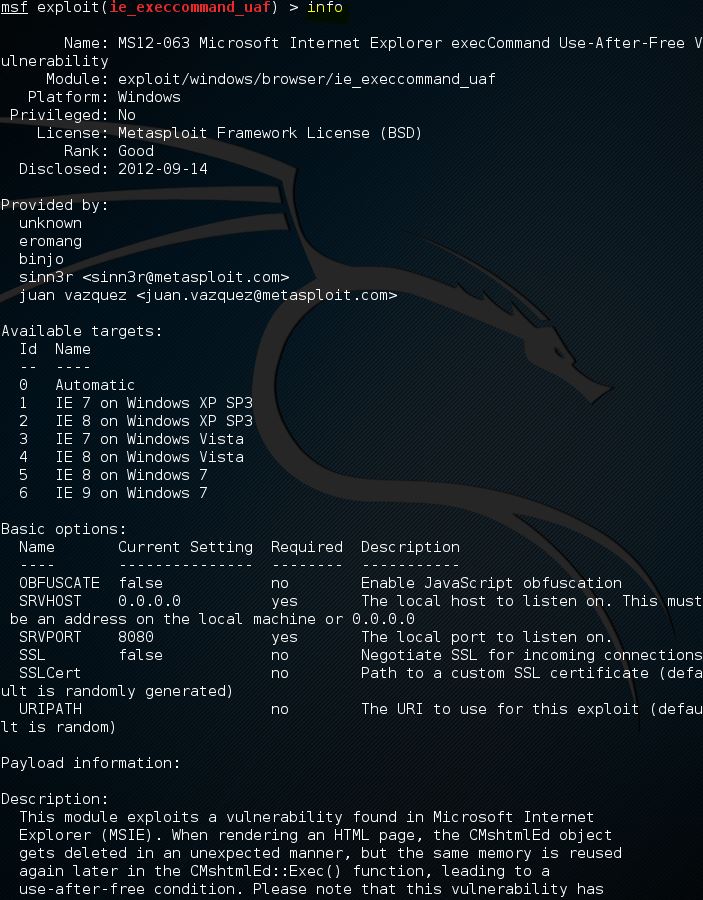
When an exploit is selected with the use command we can retrieve information like the name, platform, author, available targets and a lot more by using the info command. In the following screenshot we’ve use the info command on an exploit named ie_execcommand_uaf:
Search command
As of this writing Metasploit contains over 1.500 different exploits and new ones are added regularly. With this number of exploit the search function, and knowing how to use it, becomes very important. The easiest way of using the search function is by issuing the command search followed by a search term, for example flash to search for exploits related to Flash player. By using the search command Metasploit will search for the given search term in the module names and description as following:
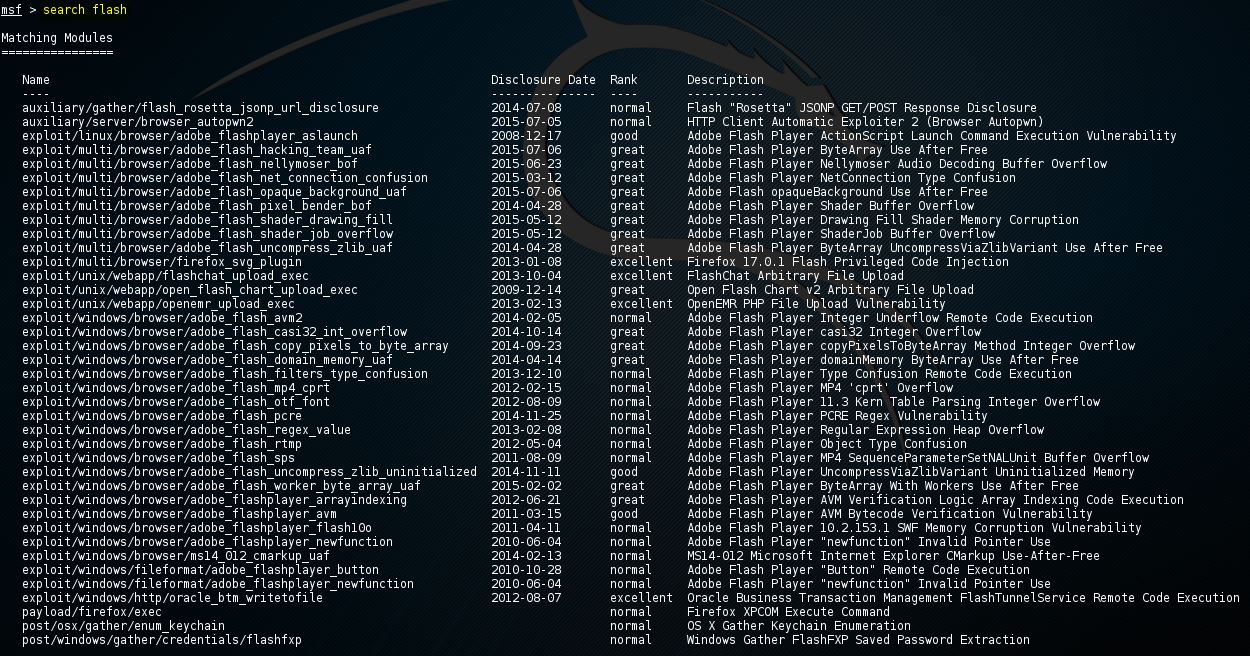
As expected there are a lot of exploits related to the often vulnerable Flash player software. The list also includes CVE-2015-5122 Adobe Flash opaqueBackground Use After Free zero-day which was discovered in the Hacking Team data breach last year.
Searching with exploits with keywords
You can also use the search command with a keyword to search for a specific author, an OSVDB ID or a platform. The ‘help search’ command displays the available keywords in the msfconsole as following:
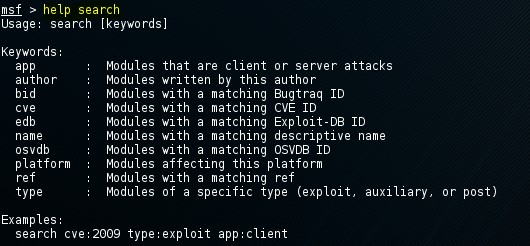
The usage of the search command with a keyword is pretty straight forward and displayed at the bottom of the help text. The following command is used to search for modules with a CVE ID from 2016:
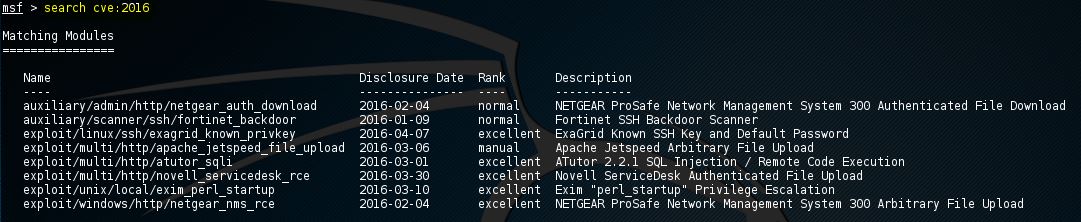
msf > search cve:2016
This returns us all exploits with a CVE ID from 2016 including and auxiliary module scanner for the very recent Fortinet firewall SSH backdoor:
Metasploit commands for exploits
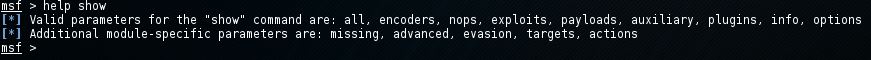
In the previous chapter we’ve learned the Metasploit commands to activate an exploit on the msfconsole and change the command line context to the exploit with the use command. Now we will be looking at how to show the exploit parameters and how to change them with the set command. We will also be looking at how to show the payloads, targets, advanced and evasion options. The help show command will display the available parameters for the show command:
Show options
The show options command will show you the available parameters for an exploit if used when the command line is in exploit context. Let’s use the adobe_flash_shader_drawing_fill exploit and have a look at the options with the following command:
msf > Use exploit/multi/browser/ adobe_flash_shader_drawing_fill
Followed by the show options command:
msf > show options
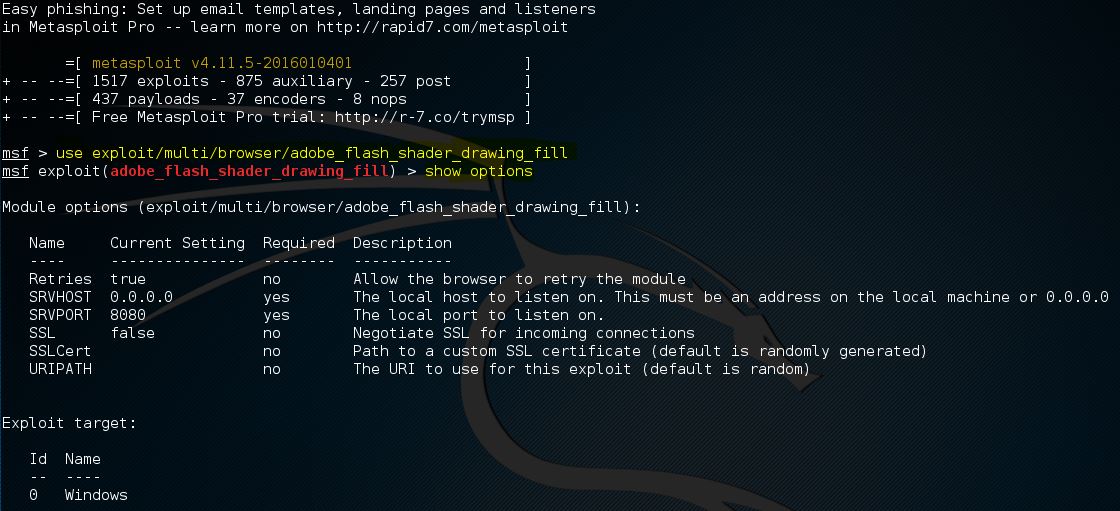
The Flash exploit contains a total of 6 options from which only 2 are required:
- Retries
- SRVHOST (Required)
- SRVPORT (Required)
- SSL
- SSLCert
- URLPath
Note that the show options command is returning the current selected target below the module options. The default target is 0 which is Windows for the selected exploit.
Use the set command followed by the option name and the new value to change the default values:
Set SRVHOST 192.168.0.100 to change the SRVHOST value to 192.168.0.100
Set SRVPORT 80 to change the port from 8080 to 80
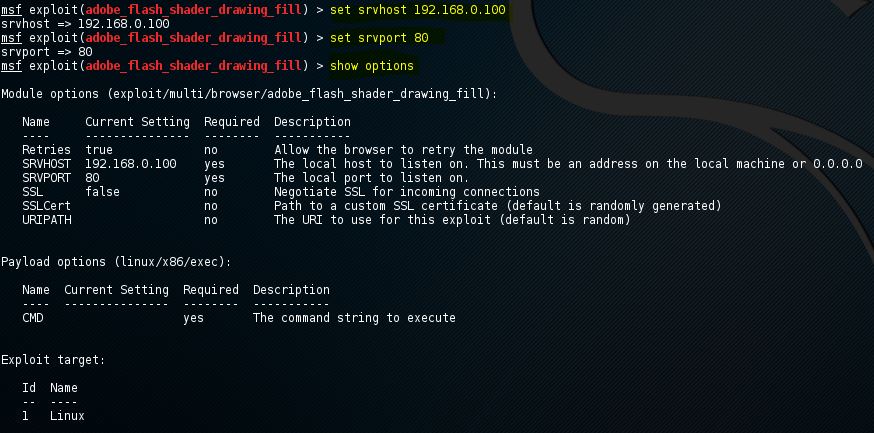
By using the show options command again you can verify that the SRVHOST and SRVPORT values have been changed. You can change Boolean values by using the set command with option name and true or false.
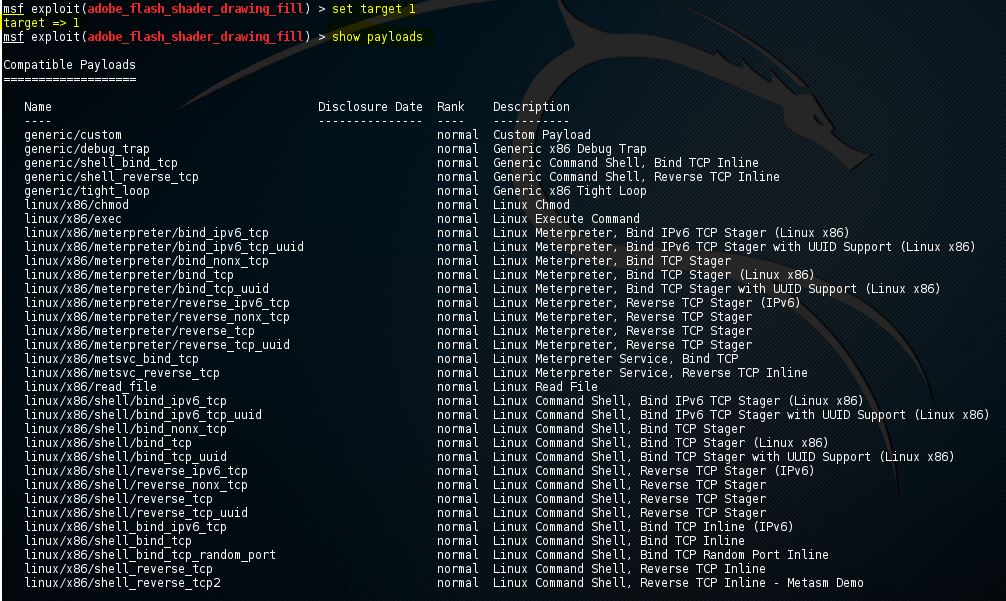
Show payloads
When we use the show payloads command the msfconsole will return a list of compatible payloads for this exploit. In our flash player exploit example it will return quite a few compatible payloads:
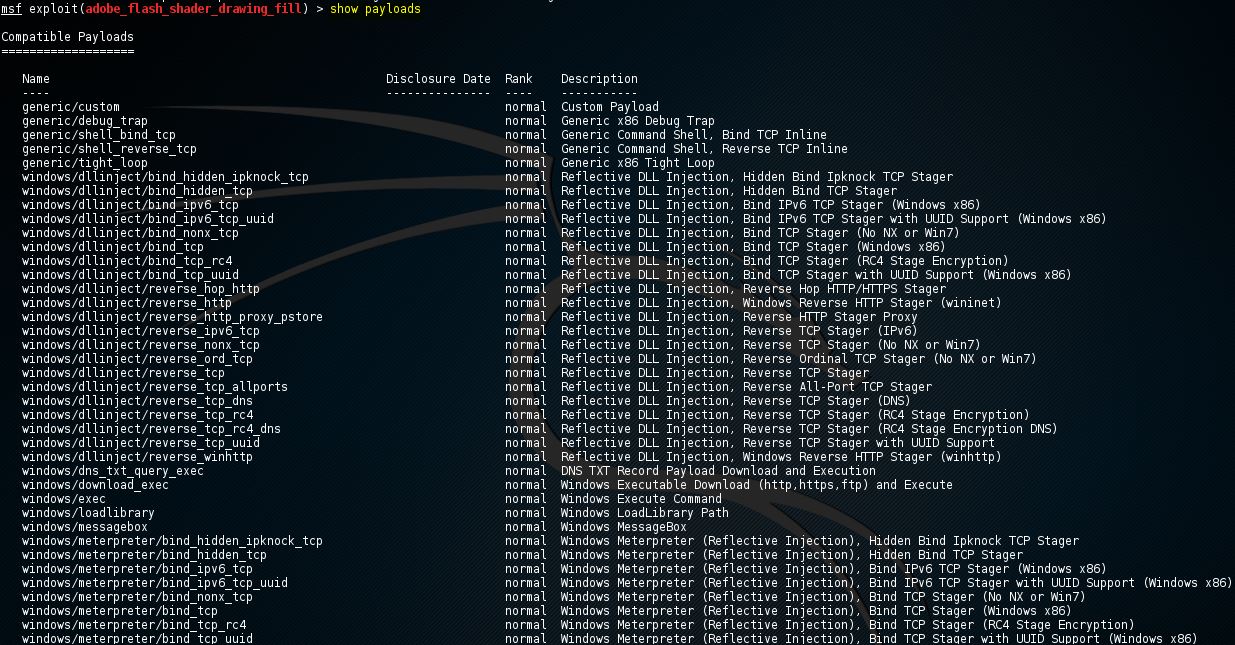
To use a certain payload you need to use the set command followed by the payload name:
Set payload linux/x86/exec
![]()
Show targets
The show targets command will return a list of operating systems which are vulnerable to the selected exploit. When we run the command we get the following output for the adobe_flash_shader_drawing_fill exploit:
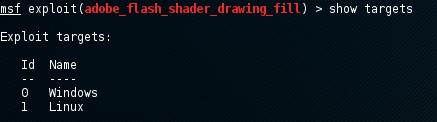
This exploit targets both Windows and Linux operating systems. Note that we can use the info command to get additional info about this exploit and targets.
To set a target we can use the command set followed by the target ID:
set target 1
By setting the target the list of payloads will be reduced a lot because only payloads will be shown which are compatible with the target:
Show advanced
By using the show advanced command we can have a look at the advanced options for the exploit.
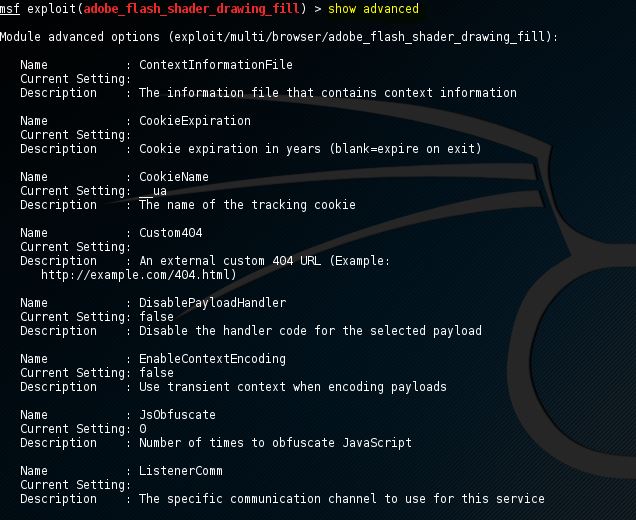
Use the set command followed by the advanced parameter and the new value to change the advanced settings:
Set displayablepayloadhandler true
![]()
Show encoders
The show encoders command will return the compatible encoders. Encoders are used to evade simple IDS/IPS signatures that are looking for certain bytes of your payload. We will be looking at encoders in detail in a later chapter of the Metasploit tutorials.
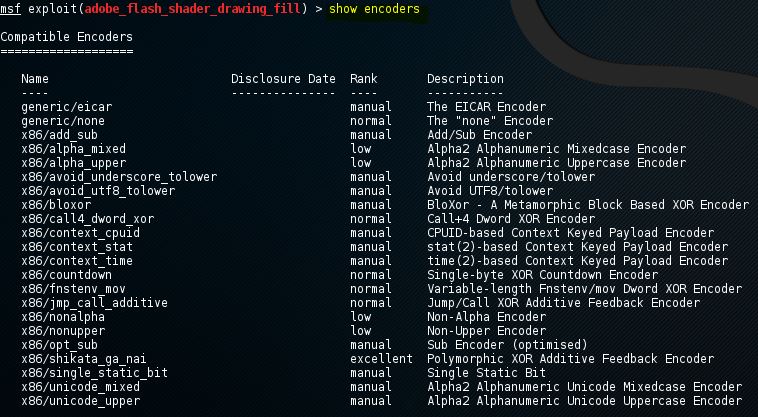
To use an encoder use the set command followed by the name of the encoder.
Show nops
The show nops command will return a list of NOP generators. A NOP is short for No Operation and is used to change the pattern of a NOP sled in order to bypass simple IDS/IPS signatures of common NOP sleds. The NOP generators start with the CPU architecture in the name. We will be looking at NOPS in a later chapter of this tutorial.
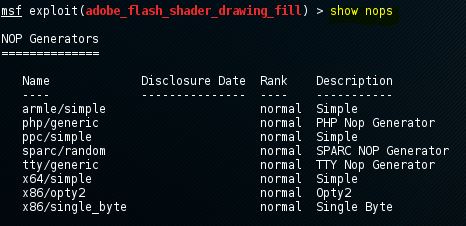
To use a NOP generator use the set command followed by the name of the NOP generator. When the exploit is launched the NOP sleds will be taken from the NOP generator.
Show evasion
The show evasion command returns a list of available evasion techniques.
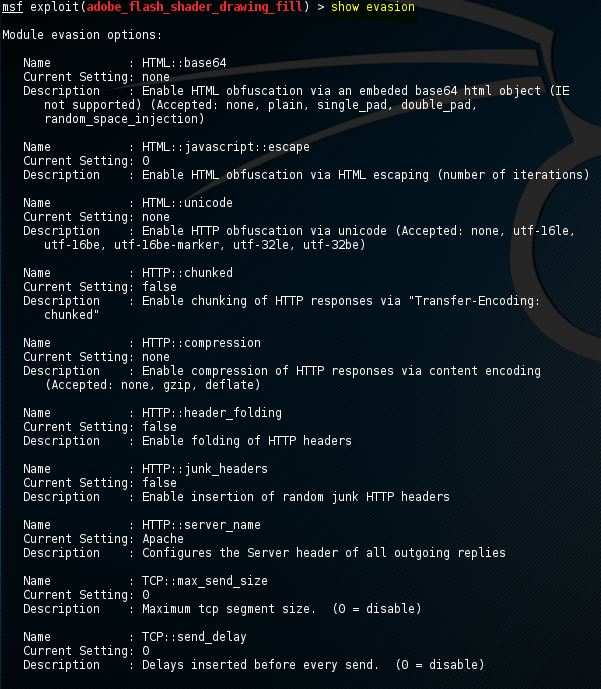
To change evasions settings use the set command followed by the evasion parameter and the new value.

Metasploit commands for exploit execution
When all the required options have been set for the exploit, including a payload and advanced settings like a NOP generator, evasion options and encoding, the exploit is ready to be executed. The exploit can be executed using two commands: run and exploit. Just type run or exploit in the msfconsole and the exploit will run.
This will conclude the Metasploit commands tutorial for now. If you have questions regarding any of the mentioned or non mentioned commands, please ask them using the comment functionality below this post. In the next Metasploit tutorial we will enumerating the Metasploitable 2 machine. After that we will be doing a vulnerability assessment with the gathered information. If you haven’t installed Metasploitable 2 yet, you can follow the Metasploitable 2 installation tutorial first.
Hacking Courses on Udemy
Bug Bounty – An Advanced Guide to Finding Good Bugs
Real World Bug Bounty Techniques

Website Hacking / Penetration Testing & Bug Bounty Hunting
Become a bug bounty hunter! Hack websites & web applications like black hat hackers and secure them like experts.


16 Comments
Can you include a way to close out the share options? They’re covering up the content.
Thanks for the feedback. I have made them smaller and you can hide them now using the << button.
my msfconsole broke down after i upgraded
check your repositories and upgrade your system
how to start meterpreter again in my windows target if i exit my msfconsole terminal ?
If you didn’t install any persistence mechanisms on the target then you’ll have to exploit the vulnerability again in order to get shell.
Every time I am trying to exploit. It’s often showing “Exploit completed but no session is created”. Could u plz help me to fix this.
Thankz in advance
This can be caused by many reasons, maybe you can sent some more information?
Maybe, you aren’t running the right commands
Hi ,,, and thank you for this useful information.
when i do every thing and try to exploit it at the end i see this error : Handler failed to bind myip:4444
and set the reverse handler into 0.0.0.0:4444.
please help what can i do?
Hi,
You’re welcome! Regarding the connection issues: you’ve probably specified incorrect settings for the LHOST parameter.
Thank you for your answer
Can you tell me how can i get the right LHOST for this?
You’re welcome!
Set the LHOST to the right IP that is able to receive the incoming connection and specify a port that is not in use by any other service as LPORT.
Hi, thank you for the very helpful tutorial. I initially got this error message:
[-] Exploit failed: The following options failed to validate: CMD.
[*] Exploit completed, but no session was created.
I then referred to this page: https://dev.metasploit.com/pipermail/framework/2010-March/005824.html which indicated that I needed to add “set CMD cmd.exe”.
Then it began to work (I think). I got this message:
[*] Exploit running as background job 1.
[*] Using URL: http://xxx.xxx.xxx.xxx:80/dno1wMbo
[*] Server started.
However, it’s stuck here forever and nothing has happened since. I doubt it should be taking this long. Anyone know what went wrong?
Hello, about this SESSION thing everytime i run an exploit it says no session started . Can someone pls help me
Hello
I have a kali linux with metasploit and armitage. It works fine when I use the default IP (12.0.0.1) to connect, but using the eth0 IP returns a connection error (connection refused).
meaning I m not able to connect from armitage located in another computer
what can I do to solve the issue?
Thanks